PowerTriage Windows
Native and portable forensic triage for Windows systems. Designed for real incident response scenarios, Live Response, and post-mortem analysis.

Native and portable forensic triage for Windows systems. Designed for real incident response scenarios, Live Response, and post-mortem analysis.

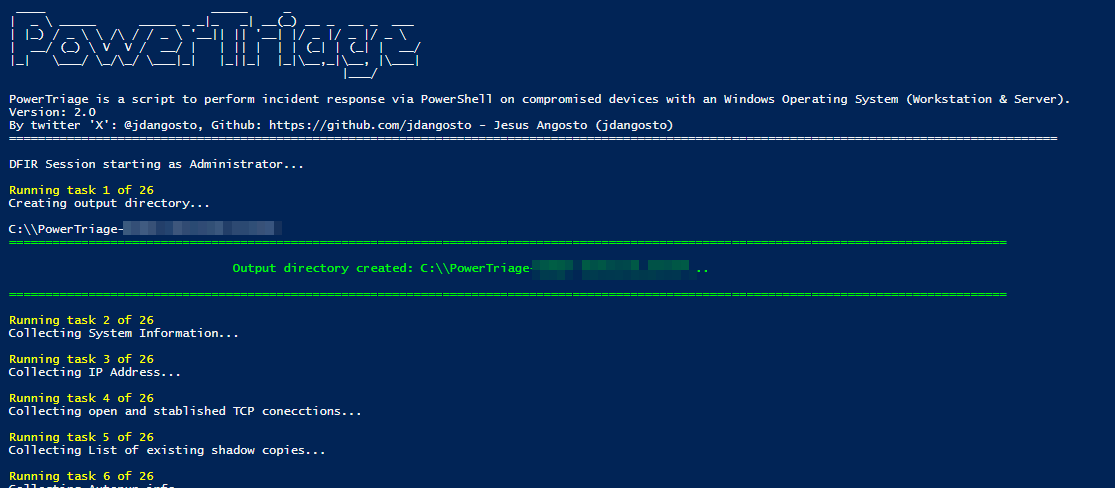
PowerTriage Windows is a forensic acquisition and triage tool developed in PowerShell for Windows systems (10, 11, and Server). It allows collecting relevant system artifacts quickly and structurally without requiring installation or external dependencies.
It is designed for direct execution on compromised systems, EDR/XDR environments, or offline analysis from mounted volumes.
PowerTriage Windows prioritizes portability, speed, and traceability during a forensic investigation, facilitating the acquisition of context in the early stages of an incident.
PowerTriage Windows is oriented towards DFIR teams, SOC, and incident response.
Prefetch, Amcache, ShimCache, BAM/DAM, and process execution evidence.
Jump Lists, Recent Files (LNK), ShellBags, Recycle Bin, and Profiles.
Active Connections (TCP/UDP), DNS Cache, ARP Table, Routes, and Firewall Rules.
History, Cookies, and Logins from Chrome, Edge, Firefox, Opera, and Brave.
Outlook (OST/PST), Logs and Metadata from OneDrive, Teams, Google Drive, and Dropbox.
Event Logs (Security, Sysmon, RDP), Services, Scheduled Tasks, Autoruns, and USB History.
Rapid collection of key artifacts for immediate context.
Complete collection for deeper forensic analysis.
Selective execution of modules according to the investigation.
Analysis from mounted volumes or images.
Structured results ready for subsequent analysis.
PowerTriage Windows is part of the PowerForensics ecosystem as an acquisition and triage component. The collected data serves as a basis for temporal analysis, correlation between systems, and broader investigations.
Consult requirements, execution parameters, and usage examples.